Microsoft’s Defender Security Research Team has disclosed a severe vulnerability in the EngageLab SDK, a widely used third-party Android push notification tool, that could have allowed malicious apps to bypass Android’s security sandbox and steal private data from crypto wallets and other applications. Over 30 million crypto wallet app installations were affected, with total exposure exceeding 50 million installations when non-wallet apps using the same SDK are included.
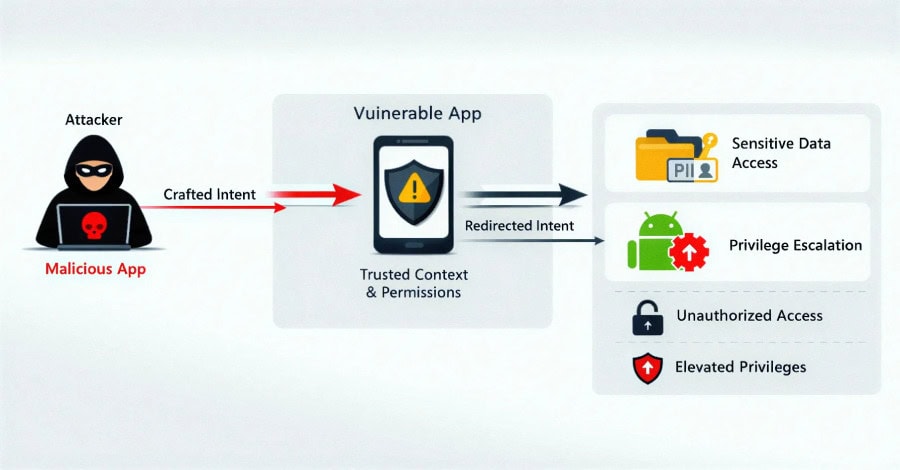
The EngageLab SDK is used by Android developers to manage push notifications and real-time in-app messaging. It functions as an integrated library that provides APIs for handling communication tasks. Microsoft identified the vulnerability in version 4.5.4 of the SDK and described it as an “intent redirection” flaw, a type of vulnerability where an attacker manipulates the content of an intent sent by a vulnerable app, leveraging that app’s trusted permissions to gain unauthorized access to protected components and sensitive data.
The specific issue was traced to an exported activity called MTCommonActivity that gets automatically added to an application’s Android manifest after the build process. Because this component only appears in the merged manifest generated post-build, developers often miss it during development. But in the final APK, the activity remains exported and accessible to any other app installed on the same device. A malicious app installed through other means could exploit this to access internal directories associated with the vulnerable app, gaining unauthorized access to personally identifiable information, user credentials and financial data.
The impact was particularly severe in the crypto and digital wallet space. Microsoft confirmed the flaw in multiple apps on the Google Play Store before disclosure but did not name the affected apps. All detected apps using vulnerable versions of the SDK have since been removed from the Play Store.
Microsoft reported the vulnerability to EngageLab in April 2025 and also notified the Android Security Team in May 2025 due to the Play Store distribution. EngageLab released a patched version, 5.2.1, on November 3, 2025, which fixed the issue by making the vulnerable component non-exported, blocking access from other apps.
Microsoft confirmed there is no evidence that the vulnerability was ever actively exploited in the wild. However, the company warned that even small flaws in upstream third-party libraries are able to have cascading effects across millions of devices, particularly in high-value sectors like digital asset management.
“Apps increasingly rely on third-party SDKs, creating large and often opaque supply-chain dependencies,” Microsoft said. “These risks increase when integrations expose exported components or rely on trust assumptions that aren’t validated across app boundaries.”
For developers using the EngageLab SDK, the advice is to update to version 5.2.1 or later immediately and to review the merged Android manifest after every build to identify any components or permissions introduced by third-party libraries that could affect security.