Social media share links contain more than just a URL. When users tap “copy link” on a post, the generated link often silently encodes personal metadata, including the sharer’s username, country, and a timestamp, without any visible indication to the user.
A new open-source tool called Sharetrace has brought this practice to light by decoding that embedded data. The tool works across a wide range of platforms, including Instagram, TikTok, Telegram, Discord, Perplexity, Substack, Suno, and ChatGPT.
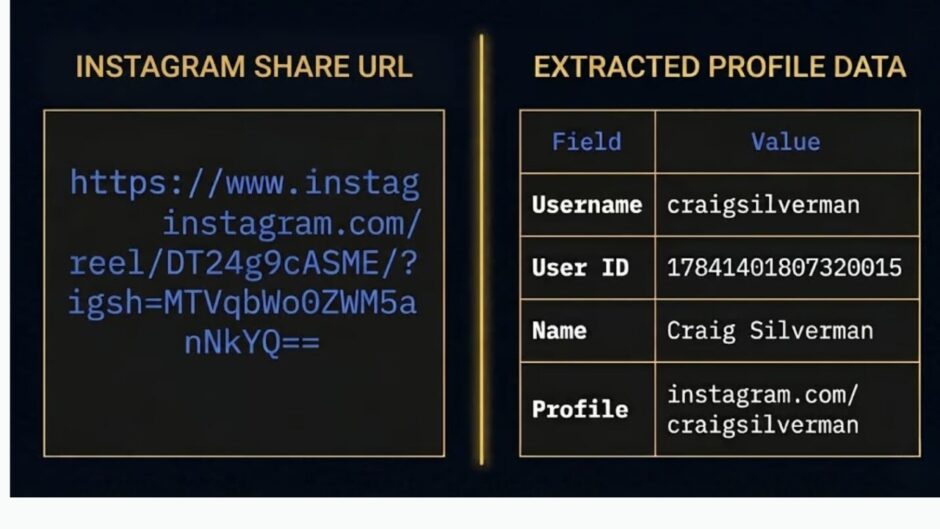
In a test on an Instagram Reel share link, Sharetrace successfully extracted the sharer’s username, numeric user ID, display name, and full profile URL, all from a link that would appear completely harmless to the average user. The findings were exposed by the investigative journalist Craig Silverman.
The discovery raises immediate privacy concerns. Users who share links publicly, in group chats, or with unknown contacts may be unknowingly exposing identifying information tied to their accounts. The practice also carries serious implications for journalists, activists, researchers, and whistleblowers who rely on a degree of anonymity when distributing content or sources online.
What makes this particularly concerning is how routine the behavior is. Copying and sharing a link is one of the most common actions performed on any platform, yet most users have no reason to suspect the resulting URL carries a fingerprint back to their account.
Platforms have long embedded tracking parameters in URLs for analytics and attribution purposes, but the inclusion of personally identifiable information, such as usernames and account IDs, goes a step further. It means that anyone who receives a shared link can potentially identify exactly who sent it, even if that person never intended to reveal their identity.
Sharetrace is available as an open-source project, allowing researchers and privacy advocates to inspect and expand its decoding capabilities independently.