Cybersecurity researchers have exposed a stealthy botnet called Masjesu that has been operating as a DDoS-for-hire service since it first surfaced in 2023. The botnet is marketed on Telegram and targets a wide range of IoT devices including routers and gateways across multiple hardware architectures. It deliberately avoids targeting IP ranges belonging to the U.S. Department of Defense to reduce the risk of triggering law enforcement attention, a strategy designed to keep the operation alive for as long as possible.
The findings come from a report published by Trellix security researcher Mohideen Abdul Khader F. The botnet is also known as XorBot due to its use of XOR-based encryption to conceal strings, configurations and payload data. It was first documented by Chinese security vendor NSFOCUS in December 2023, which linked it to an operator using the alias “synmaestro.”
A later version of the botnet observed in late 2024 had expanded significantly. It added 12 different command injection and code execution exploits targeting routers, cameras, DVRs and NVRs from D-Link, Eir, GPON, Huawei, Intelbras, MVPower, NETGEAR, TP-Link and Vacron. New modules were also added to carry out DDoS flood attacks. The most recent iteration tracked by Trellix shows Masjesu now markets the ability to carry out volumetric DDoS attacks against content delivery networks, game servers and enterprises.
Attacks mounted by the botnet primarily originate from Vietnam, Ukraine, Iran, Brazil, Kenya and India, with Vietnam accounting for nearly 50% of the observed traffic.
Once deployed on a compromised device, the malware creates and binds a socket with a hard-coded TCP port (55988) to allow the attacker to connect directly. If this operation fails, the attack chain is immediately killed. If it succeeds, the malware sets up persistence, ignores termination-related signals and stops commonly used processes like wget and curl, possibly to disrupt competing botnets already running on the same device. It then connects to an external server to receive DDoS attack commands.
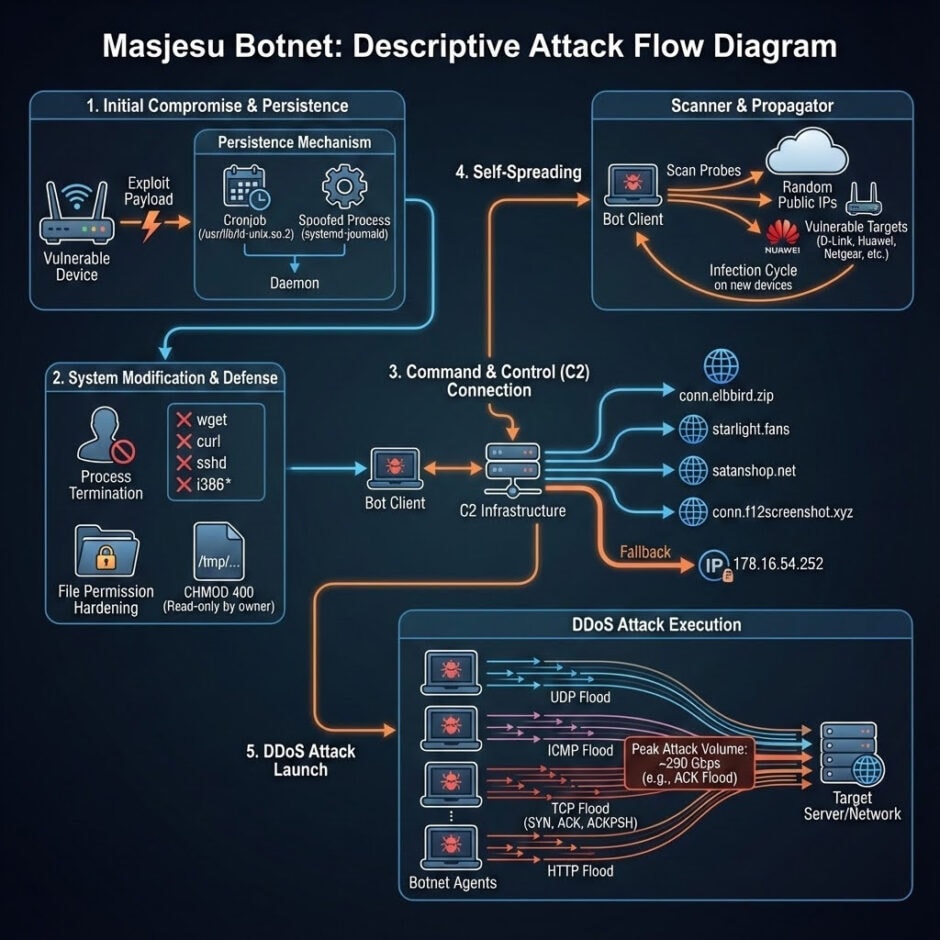
Masjesu also has self-propagating capabilities. It probes random IP addresses for open ports and attempts to compromise additional devices to expand its infrastructure. One notable addition to its list of targets is Realtek routers, which it scans on port 52869, a port associated with the Realtek SDK’s miniigd daemon. Other botnets including JenX and Satori have used the same approach in the past.
The botnet’s operators appear to use Telegram as their primary channel for recruitment and promotion. NSFOCUS noted in November 2024 that the controllers were “increasingly inclined to use social media platforms such as Telegram as the main channels for recruitment and promotion, attracting target customers through initial active promotional activities.”
The deliberate avoidance of sensitive government and military targets is a calculated survival strategy. By staying below the threshold that would trigger significant legal or law enforcement attention, the operators extend the botnet’s operational lifespan while continuing to profit from commercial DDoS attacks.
For organizations running IoT devices from the affected manufacturers, the standard advice applies: update firmware, change default credentials, disable unnecessary remote management features and monitor network traffic for unusual outbound connections. The list of targeted manufacturers, D-Link, Huawei, NETGEAR, TP-Link and Realtek, covers a significant share of consumer and small business router deployments globally.