Hackers are targeting employees through Microsoft Teams in a new phishing campaign designed to gain remote access to corporate computers and deploy backdoor malware. The attacks have primarily targeted workers in financial and healthcare organizations and rely heavily on social engineering rather than technical exploits.
Researchers say attackers contact victims directly through Microsoft Teams messages while impersonating IT support staff or trusted colleagues. The messages claim there is a technical issue that requires immediate assistance and instruct employees to open Quick Assist, a legitimate Windows remote support tool.
“The malware extracts and decodes the leftmost label to recover command/configuration data, then proceeds accordingly,” explains BlueVoyant, a third-party risk assessment company. “Using DNS MX records helps the traffic blend in and can evade controls tuned to detect TXT-based DNS tunneling, which may be more commonly monitored.”
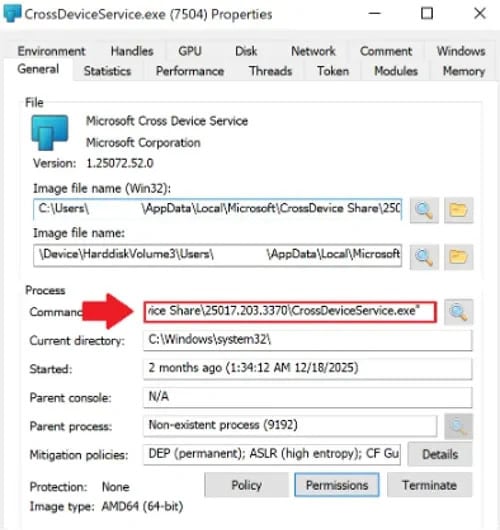
Quick Assist allows one user to view or control another computer remotely. Once the victim accepts the session request, the attacker gains full access to the system and installs a previously undocumented malware strain called A0Backdoor. The malware establishes persistent access and allows attackers to execute commands, move across networks, and potentially steal sensitive data.
The attackers deliberately use Quick Assist because it is a Microsoft-signed tool built into Windows systems. Since the utility is legitimate and widely used for technical support, it rarely triggers antivirus alerts or endpoint detection systems. This allows attackers to bypass many traditional security defenses.
Security researchers say collaboration platforms such as Microsoft Teams are becoming increasingly attractive targets for phishing campaigns. Many organizations have strengthened email security with filtering systems and employee training, making email-based phishing easier to detect.
Messages sent through internal communication platforms can appear more trustworthy to employees. Workers often assume that messages received through Teams originate from colleagues or internal support staff, making them more likely to follow instructions without questioning them.
The A0Backdoor campaign is part of a broader pattern of attackers shifting toward workplace collaboration tools as entry points into corporate networks. Several cybercrime groups have previously used Teams-based phishing to distribute malware or establish access before launching ransomware attacks.
Security experts recommend restricting Quick Assist sessions through administrative policies and limiting who can initiate remote access requests. Organizations are also advised to monitor authentication logs for unusual activity and expand employee security training to include social engineering attempts conducted through workplace messaging platforms rather than focusing only on email phishing.




















