A China-linked threat group known as Storm-1175 is using a mix of zero day and known vulnerabilities to carry out fast moving cyber attacks and deploy Medusa ransomware on exposed systems.
Security researchers report the group targets internet facing infrastructure and moves quickly once access is gained. The attackers combine newly discovered flaws with older unpatched weaknesses to break into systems and escalate control.
“The threat actor’s high operational tempo and proficiency in identifying exposed perimeter assets have proven successful, with recent intrusions heavily impacting healthcare organizations, as well as those in the education, professional services, and finance sectors in Australia, the United Kingdom, and the United States,” the Microsoft Threat Intelligence team said.
Microsoft data shows the group can move from initial access to data theft and ransomware deployment in as little as 24 hours. This short window reduces the chance of detection and response.
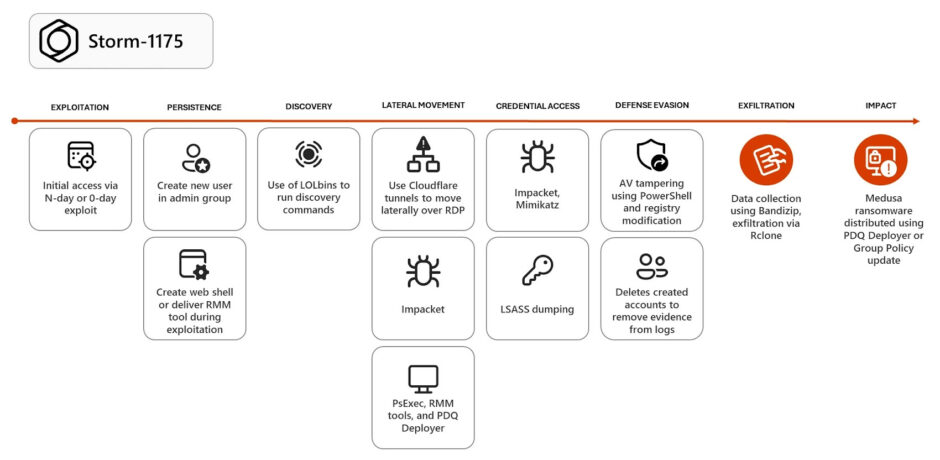
The attacks rely on chaining vulnerabilities. Zero day flaws provide initial entry, while known vulnerabilities help attackers expand access inside networks. This approach increases success rates, especially against organizations with delayed patching cycles.
Once Medusa is deployed, it encrypts systems and demands payment for recovery. The group has used similar tactics in earlier campaigns, often targeting enterprise systems and critical infrastructure. Security researchers note an increase in zero day exploitation, with attackers focusing on enterprise software and edge devices exposed to the internet.
Since 2023, Storm-1175 has been linked to the exploitation of more than 16 vulnerabilities, namely:
- CVE-2023-21529 (Microsoft Exchange Server)
- CVE-2023-27351 and CVE-2023-27350 (Papercut)
- CVE-2023-46805 and CVE-2024-21887 (Ivanti Connect Secure and Policy Secure)
- CVE-2024-1708 and CVE-2024-1709 (ConnectWise ScreenConnect)
- CVE-2024-27198 and CVE-2024-27199 (JetBrains TeamCity)
- CVE-2024-57726, CVE-2024-57727, and CVE-2024-57728 (SimpleHelp)
- CVE‑2025‑31161 (CrushFTP)
- CVE-2025-10035 (Fortra GoAnywhere MFT)
- CVE-2025-52691 and CVE-2026-23760 (SmarterTools SmarterMail)
- CVE-2026-1731 (BeyondTrust)
Storm-1175 appears financially motivated rather than purely state directed, though its links to China-based operations remain under investigation. The group focuses on speed, automation, and high impact targets, which aligns with recent ransomware trends.
The attacks such as these are a constant reminder that there is a persistent gap in patch management. Organizations that delay updates or expose critical systems online face higher risk, especially when attackers combine new exploits with known weaknesses.