You would not expect a design flaw like this one from Cisco. Even if a flaw did occur you would expect them to at least spot it before shipping the product. But this is very much true and wasn’t spotted early on. So what exactly happened, you might ask. In 2013, Cisco had to issue a field notice warning of a problem with its very expensive 48-port models of 3650 and 3850 Series Switches, which are used in many data centers around the world. That field notice explained in detail a major problem with their switches, discovered after they were released: they were vulnerable to system reset and plugging in a cable could wipe them entirely in just a few seconds.
Until a few days ago, regular citizens had no idea about this ordeal until someone pointed the flaw and tweeted it out. So much for getting away with it easily.
Hilarious Cisco design flaw http://t.co/0McVHiQPGD (that button wipes the device when held in) HT @Nank_ pic.twitter.com/m7JM2qrPNR
— Liam (@liamosaur) September 7, 2015
In the aforementioned models, the system factory reset button is directly above Port 1. Now, the “snagless” ethernet cable models have a little protective boot that keeps you from accidentally breaking or pressing the release tab, which would render the cable useless. Check this cable for instance:
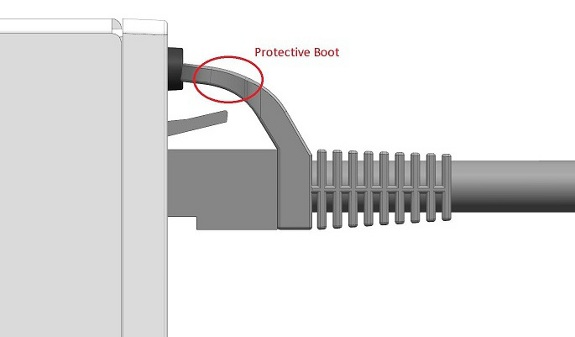
Do you see anything else? The protective boot is pressing the factory reset button. So whenever you insert a cable into the Port 1, you’re also resetting the system.
Now these kind of switches are not commonly used in homes but are designed for data centers. The whole data center, or the network, wouldn’t just shut down but you can imagine the chaos that would follow if a design flaw like this were to reset their systems.
How this major flaw crawled into the market under the supervision of Cisco, the world’s top networking equipment manufacturer, is unfathomable. What’s more disappointing is the approach used by Cisco to fix this problem: buy an ethernet cable without the protective boot or cut off the boot and be done with it.
The problem can also be fixed by disabling the button, but the fact remains that such design flaws do creep into the market. While you may not be able to relate to the potential mayhem this could cause, a network engineer would probably know the gravity of this problem.




















