Cybersecurity researchers have discovered a new Lua-based malware created years before the notorious Stuxnet worm that aimed to sabotage Iran’s nuclear program by destroying uranium enrichment centrifuges. According to a new report published by SentinelOne, the previously undocumented cyber sabotage framework dates back to 2005 and primarily targets high-precision calculation software to tamper with results. It has been codenamed fast16.
Predates Stuxnet by Five Years
Fast16 is estimated to predate Stuxnet, the world’s first known digital weapon designed for disruptive actions, by at least five years. While Stuxnet is widely attributed to the United States and Israel and later served as the architectural foundation for the Duqu information-stealing rootkit, fast16 appears to have emerged much earlier.
It also precedes the earliest known samples of Flame, another sophisticated malware that was discovered in May 2012 incorporating a Lua virtual machine to realize its goals. The discovery makes fast16 the first strain of Windows malware to embed a Lua engine.
Discovery Through Shadow Brokers Leak
SentinelOne said it made the discovery after it identified an artifact named svcmgmt.exe that at first blush appeared to be a generic console-mode service wrapper. The sample has a file creation timestamp of August 30, 2005 per VirusTotal, to which it was uploaded more than a decade later on October 8, 2016.
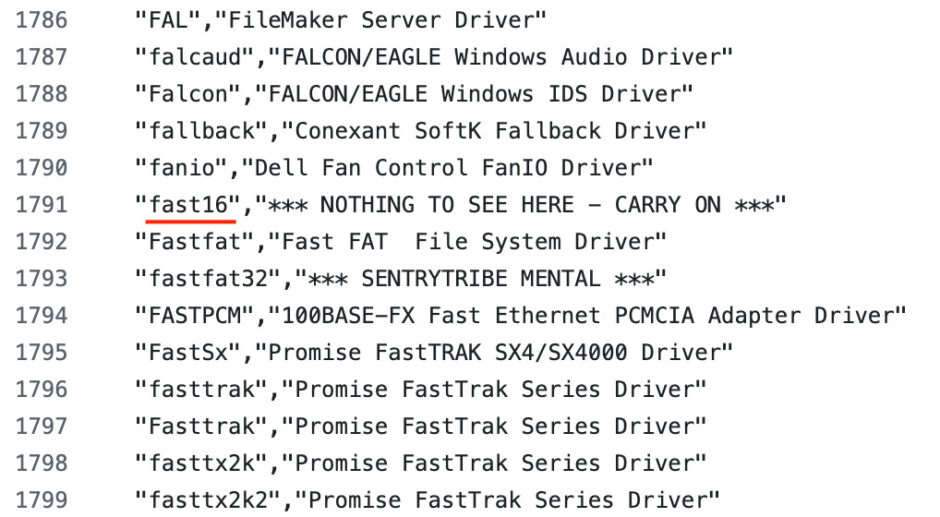
However, deeper investigation revealed an embedded Lua 5.0 virtual machine and an encrypted bytecode container along with various other modules that bind directly into Windows NT file system, registry, service control and network APIs. The implant’s core logic resides in the Lua bytecode, with the binary also referencing a kernel driver fast16.sys via a PDB path.
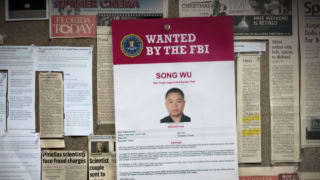
SentinelOne uncovered a reference to the string fast16 in a text file called drv_list.txt that included a list of drivers designed for use in advanced persistent threat attacks. The nearly 250KB file was leaked by The Shadow Brokers in 2016 and 2017. The mysterious hacking group published vast troves of data allegedly stolen from the Equation Group, an advanced persistent threat group with suspected ties to the United States National Security Agency.
Targeting Engineering Software
By combining this payload with self-propagation mechanisms, the attackers aim to produce equivalent inaccurate calculations across an entire facility. The kernel driver is responsible for the precision sabotage, targeting executables compiled with the Intel C/C++ compiler to perform rule-based patching and hijack execution flow through malicious code injections.
One such block is capable of corrupting mathematical calculations, specifically going after tools used in civil engineering, physics and physical process simulations. By introducing small but systematic errors into physical-world calculations, the framework could undermine or slow scientific research programs, degrade engineered systems over time or even contribute to catastrophic damage.
Targeting LS-DYNA and Iran’s Nuclear Program
Based on an analysis of the 101 rules defined in the patching engine, it is assessed that three high-precision engineering and simulation suites may have been the targets: LS-DYNA 970, PKPM and the MOHID hydrodynamic modeling platform. LS-DYNA, now part of the Ansys Suite, is a general-purpose multiphysics simulation software package used for simulating crashes, impacts and explosions.
In September 2024, the Institute for Science and International Security released a report detailing Iran’s likely use of computer modeling software like LS-DYNA related to nuclear weapons development based on an examination of 157 academic publications found in open-source scientific and engineering literature.
This chain of evidence assumes significance considering Iran’s nuclear program is said to have suffered substantial damage after its uranium enrichment facility in Natanz was targeted by the Stuxnet worm in June 2010. Moreover, Symantec revealed in February 2013 an earlier version of Stuxnet that was used to attack Iran’s nuclear program in November 2007, with evidence indicating it was under development as early as November 2005.
Environmental Awareness and Propagation
Fast16 comes with three distinct payloads: Lua bytecode to handle configuration and propagation and coordination logic, an auxiliary ConnotifyDLL and the fast16.sys kernel driver. It is designed to parse the configuration, escalate itself as a service, optionally deploy the kernel implant and launch a Service Control Manager wormlet that scans for network servers and propagates the malware to other Windows 2000/XP environments with weak or default credentials.
An important aspect is that the propagation only occurs when it is manually forced or common security products are not found on the system by scanning the Windows Registry database for associated registry keys. Some of the security tools it explicitly checks belong to Agnitum, F-Secure, Kaspersky, McAfee, Microsoft, Symantec, Sygate Technologies and Trend Micro.
Forces Re-evaluation of Cyber Sabotage Timeline
The latest finding forces a re-evaluation of the historical timeline of development for clandestine cyber sabotage operations, SentinelOne said, adding it shows state-backed cyber sabotage tooling against physical targets had been fully developed and deployed by the mid-2000s.
In the broader picture of APT evolution, fast16 bridges the gap between early largely invisible development programs and later more widely documented Lua and LuaJIT-based toolkits. It is a reference point for understanding how advanced actors think about long-term implants, sabotage and a state’s ability to reshape the physical world through software. Fast16 was the silent harbinger of a new form of statecraft, successful in its covertness until today.