Microsoft has issued a warning about a malware campaign that uses WhatsApp messages to compromise Windows computers. The attack has been active since February 26, 2026, and targets all 3.3 billion WhatsApp users, though the payload only affects those running Windows.
The campaign starts with a phishing message sent through WhatsApp containing a Visual Basic Script (VBS) file. If a user opens the file, it triggers a multi-stage infection chain designed to establish persistent access to the machine. The attackers rename standard Windows utilities to blend in with normal system activity, making detection harder for security software. The attack then downloads additional payloads from trusted cloud services, including AWS, Tencent Cloud and Backblaze B2. It installs malicious Microsoft Installer (MSI) packages to maintain control of the compromised system.
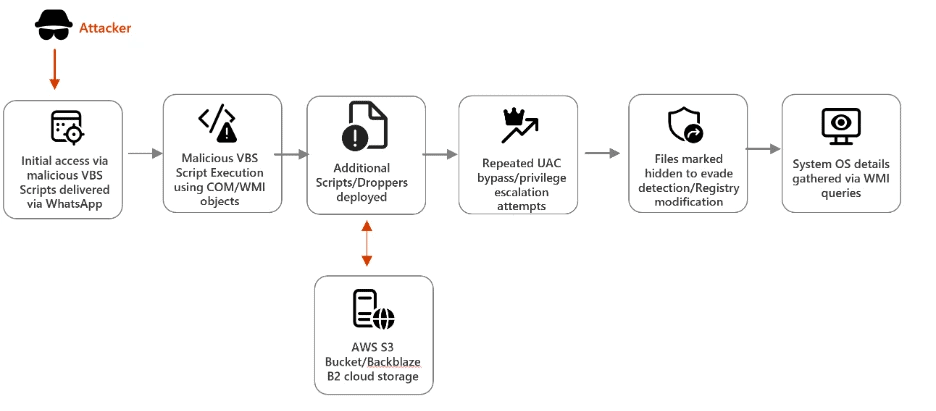
This campaign demonstrates a sophisticated infection chain combining social engineering (WhatsApp delivery), stealth techniques (renamed legitimate tools, hidden attributes), and cloud-based payload hosting. The attackers aim to establish persistence and escalate privileges, ultimately installing malicious MSI packages on victim systems.
Microsoft’s Defender Security Research team described the campaign as a combination of social engineering and living-off-the-land techniques. By relying on trusted platforms and legitimate tools, the attackers reduce visibility and increase the chances of successful execution. The end result is a backdoor that gives threat actors persistent remote access to the victim’s data.
Experts say users should only click on links or open files from people they know and trust, regardless of which messaging service they use. They add that WhatsApp provides extra information when someone messages you for the first time, including whether the person is in your contacts, where their phone number is registered and any mutual groups you share.
Security experts warn that the campaign’s reliance on trusted cloud infrastructure and standard Windows tools makes it particularly difficult to detect using traditional security methods. The entire attack chain exploits trust at every level, from the messaging platform to the operating system tools to the cloud services hosting the payloads.
WhatsApp has also rolled out Strict Account Settings, which automatically apply tighter security controls. The platform has also updated its protections against this type of attack.






















