A ransomware operation called LeakNet has shifted its initial access strategy away from purchasing stolen credentials on the black market, instead compromising legitimate websites and using them to trick visitors into infecting themselves.
The technique, known as ClickFix, works by injecting fake CAPTCHA verification prompts into hacked websites. When users visit these sites, they are instructed to copy and paste a command into the Windows Run dialog to supposedly verify they are human. The command actually executes msiexec.exe, a built-in Windows tool, to silently download and install malware. Because the victim runs the command themselves through a trusted system utility, the attack bypasses many traditional security controls.
According to a technical report published by cybersecurity firm ReliaQuest, the move represents a significant strategic evolution for LeakNet, which first appeared in November 2024 and has previously targeted industrial organizations. By moving away from initial access brokers (IABs), the group eliminates a dependency that limited how quickly and broadly it could operate. ClickFix also lowers per-victim acquisition costs and removes the bottleneck of waiting for valuable stolen accounts to appear on underground markets.
The attacks are not aimed at any specific industry. Instead, LeakNet casts a wide net, compromising websites across sectors to infect as many victims as possible.
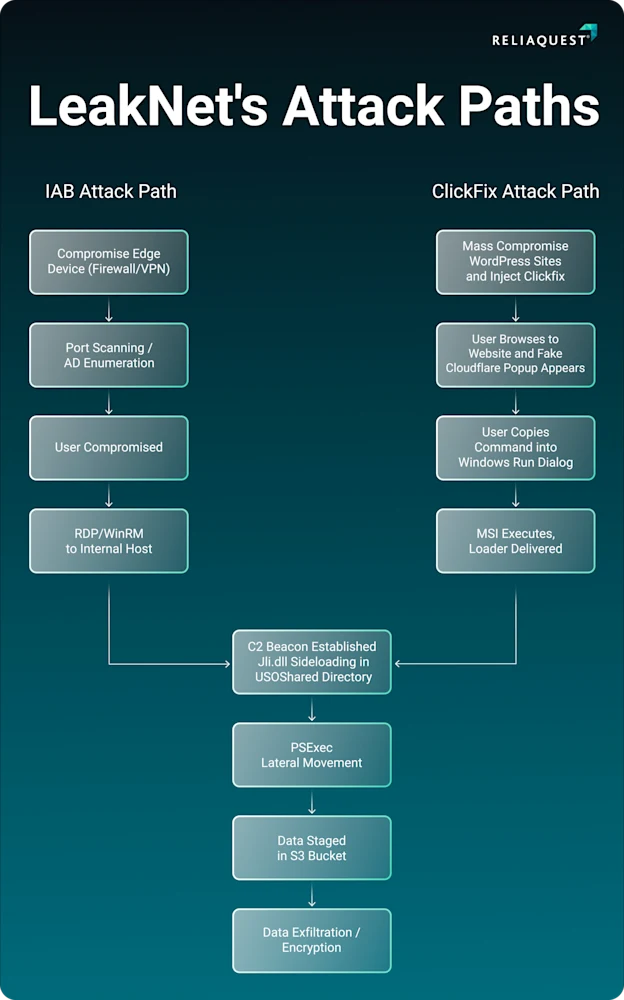
Once a machine is compromised, LeakNet deploys a loader built on the Deno JavaScript runtime, a relatively unusual choice that allows the group to execute Base64-encoded payloads directly in memory. This “bring your own runtime” approach minimizes evidence left on disk and makes detection significantly harder. The loader fingerprints the compromised system, contacts an external server for next-stage malware, and enters a polling loop that continuously fetches and executes additional code.
ReliaQuest also observed a separate intrusion attempt where attackers used Microsoft Teams-based phishing to socially engineer a user into launching a payload chain that ended with the same Deno-based loader. Whether this represents LeakNet expanding its access methods or another threat group adopting the same technique remains unclear.
After gaining access, LeakNet follows a consistent post-compromise playbook. The group uses DLL side-loading to launch malicious code, runs Windows commands like “klist” to enumerate active authentication credentials on the system, then moves laterally across the network using PsExec. Data is staged and exfiltrated to Amazon S3 buckets, exploiting the appearance of normal cloud traffic to reduce the detection footprint, before ransomware encryption begins.
The report arrives alongside findings from Google’s Threat Intelligence Group showing that ransomware remains a persistent and adaptive threat despite ongoing law enforcement disruptions.
Google identified Qilin, Akira, Cl0p, Play, SafePay, INC Ransom, Lynx, RansomHub, DragonForce, and Sinobi as the ten most active ransomware brands by victim count.
“In a third of incidents, the initial access vector was confirmed or suspected exploitation of vulnerabilities, most often in common VPNs and firewalls,” Google Threat Intelligence Group (GTIG) said, adding 77% of analyzed ransomware intrusions included suspected data theft, an increase from 57% in 2024.
Google also noted that while ransomware actors remain highly motivated, overall profitability appears to be declining, with some groups shifting their focus from large enterprises to higher-volume attacks against smaller organizations.