Four official SAP npm packages were compromised on April 29, 2026 in a supply chain attack dubbed “Mini Shai-Hulud” that injected malicious preinstall scripts to steal developer credentials, CI/CD secrets and cloud provider tokens from enterprise environments building applications on SAP’s Business Technology Platform. Security researchers at StepSecurity, Aikido Security, SafeDep, Socket and Wiz identified malicious versions of @cap-js/sqlite, @cap-js/postgres, @cap-js/db-service and mbt packages published between 09:55 UTC and 12:14 UTC containing weaponized installation hooks that execute automatically during npm install operations before package installation completes.
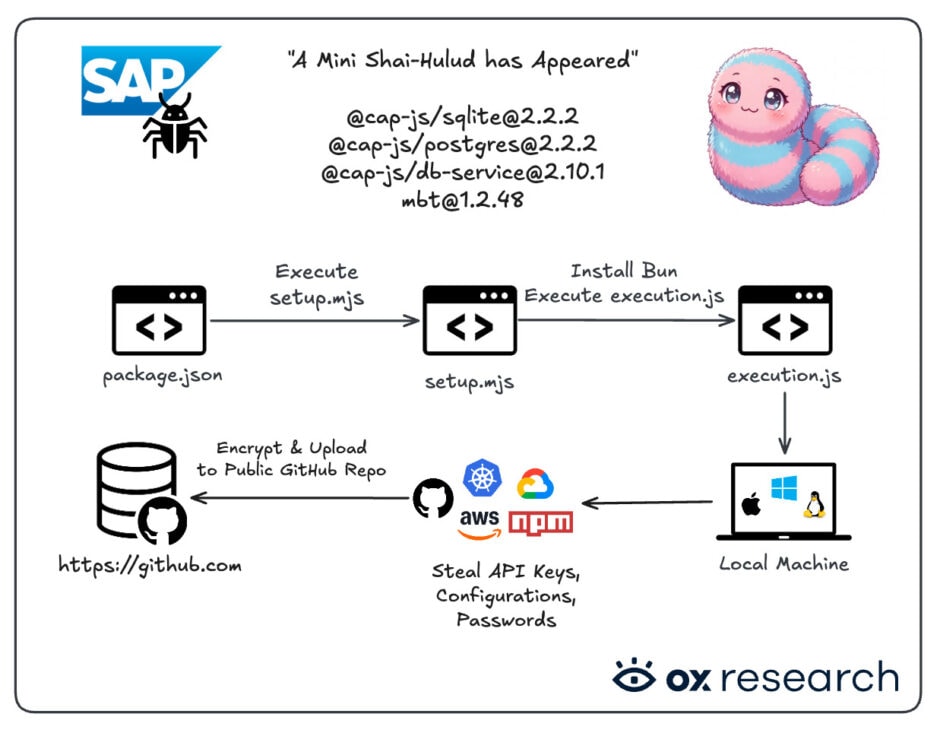
The compromised packages collectively receive approximately 570,000 weekly downloads and serve as core components of SAP’s Cloud Application Programming Model ecosystem used by enterprise development teams building cloud applications and Multi-Target Application deployment pipelines touching production SAP systems. The attack weaponized the routine npm install command by introducing a new package.json preinstall hook that runs a file named setup.mjs acting as a loader for the Bun JavaScript runtime to execute an 11.6 MB obfuscated credential stealer and propagation framework stored in execution.js.
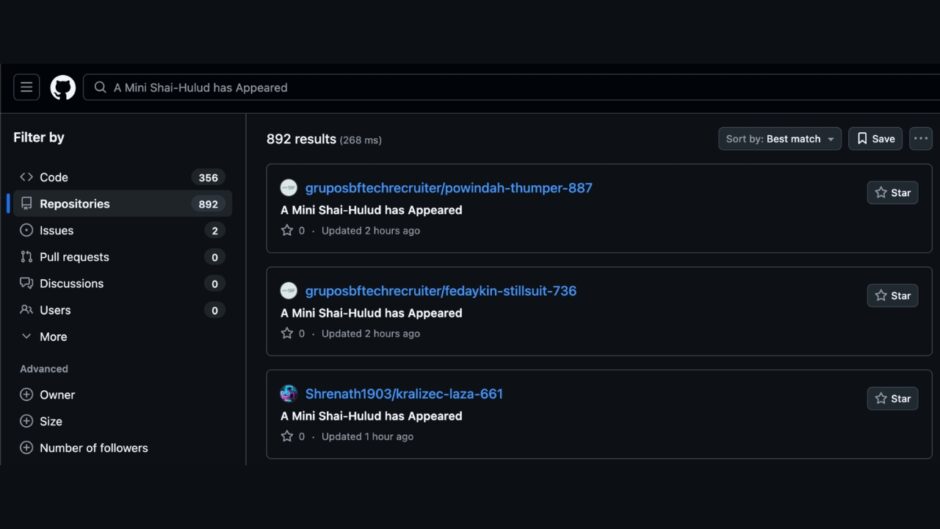
The malware harvests local developer credentials, GitHub and npm tokens, GitHub Actions secrets and cloud secrets from AWS, Azure, Google Cloud Platform and Kubernetes environments according to Aikido Security analysis. Stolen data is encrypted using RSA public key cryptography and exfiltrated to public GitHub repositories created on victims’ own accounts with the description “A Mini Shai-Hulud has Appeared,” with over 1,100 repositories displaying this signature as of April 30, 2026 indicating widespread compromise across the global developer community.
The payload includes self-propagation capabilities designed to spread through developer and release workflows by using stolen GitHub and npm tokens to inject malicious GitHub Actions workflows into victims’ repositories. Wiz researchers noted that this operation adds the ability to steal credentials from multiple browsers including Chrome, Safari, Edge, Brave and Chromium and exfiltrate passwords found there, representing functionality not present in previous TeamPCP operations. The malware also scrapes CI/CD environment variables, SSH private keys and memory-resident secrets from running processes on compromised developer machines and continuous integration runners.
Researchers assess with high confidence that TeamPCP threat actors responsible for previous Shai-Hulud campaigns compromising over 700 npm packages in late 2025 are behind this attack based on shared RSA public key used to encrypt exfiltrated secrets, overlapping encoding routines and identical region guardrails. The malware performs a system check during initial setup to determine if the compromised machine is configured for Russian language by inspecting date/time locale settings and environment language variables, terminating execution if any values begin with ‘ru’ to ensure no data is exfiltrated from Russian-speaking systems.
SAP’s official statement posted on GitHub repository cap-js/cds-dbs indicates an unauthorized actor pushed malicious commits that hijacked the release workflow and triggered unauthorized npm publications on April 29, 2026. The attacker was able to publish compromised packages because the workflow had publish permissions without any manual approval gate, with the fix implemented to gate npm publish operations behind environment reviews requiring manual authorization. The malicious versions were published from the legitimate cloudmtabot npm account which has since been suspended following the incident.
Security analysis by multiple firms suggests the attack vector involved compromising a legitimate SAP developer account and modifying a GitHub Actions workflow to exchange a GitHub OIDC token for a live npm publish token scoped to @cap-js/sqlite. The critical flaw exploited npm’s trusted publishing configuration for the package which trusted any workflow in the cap-js/cds-dbs repository rather than exclusively trusting the canonical release workflow on the main branch, meaning a push to a non-main branch provided sufficient access to obtain valid publish credentials.
SAP released clean versions of all affected packages by 13:46 UTC on April 29, 2026 published via GitHub Actions OIDC trusted publisher rather than the compromised cloudmtabot account. Organizations using SAP CAP tooling should immediately audit CI/CD pipeline dependencies, rotate all secrets present in affected environments including GitHub tokens with all scopes, npm tokens, AWS/Azure/GCP access keys and CI/CD secrets, and audit repositories for unexpected tasks.json additions in .vscode/ or .claude/ directories. Defenders should search GitHub accounts for repositories with the description string “A Mini Shai-Hulud has Appeared” indicating compromise.




















