Cybersecurity
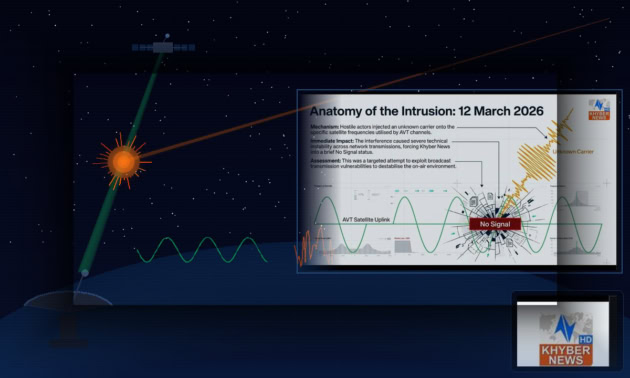
Khyber News Knocked off-air in Satellite Cyber Attack
VoidLink Malware Almost Entirely Built by AI, Experts Warn
Cybersecurity researchers have identified a new strain of malware, codenamed VoidLink, that was created almost entirely using artificial intelligence. According to a detailed analysis from…
NADRA Teams Up with HEC for National Bug Bounty Initiative
The National Database and Registration Authority (NADRA) has launched its first-ever Bug Bounty Challenge 2026, a nationwide initiative aimed at strengthening the cybersecurity of Pakistan’s…
Massive Database Breach Exposes 149M Credentials from Facebook, Instagram, Gmail and More
Cybersecurity researchers have confirmed that a massive trove of login credentials tied to Gmail, Instagram, Netflix, and dozens of other everyday platforms was left openly…
Govt of Punjab’s official X account hacked; posts reading “i hate Pakistan” and crypto links
The official X (formerly Twitter) account of the Government of Punjab was briefly compromised at about 1:00 p.m. (PKT) today, during which the profile published…
NCERT Launches Last Round of Consultation on Cybersecurity Rules
The National Cyber Emergency Response Team (NCERT) has launched a final stakeholder consultation on the revised Pakistan Information Security Framework 2025, marking the last stage…
Why This New Ransomware is Impossible for Standard Security to Stop
A newly identified Osiris ransomware variant is drawing urgent attention from cybersecurity researchers after evidence showed it can quietly slip past traditional defenses, establish persistence,…
Critical Fortinet Flaws Put Core Security Systems at Risk, CERT Warns
A set of newly disclosed critical vulnerabilities in Fortinet products is raising serious cybersecurity concerns, with national CERT (Computer Emergency Response Team) authorities warning that…
Why Your Ad Blocker Might Be Crashing Your Browser to Deliver Malware
Security researchers have uncovered a sophisticated new malware campaign that intentionally crashes web browsers to trick users into downloading malicious software, with the attack leveraging…
New Dual-Stage Malware Marks a Terrifying Milestone in Cyberthreat Evolution
Cybersecurity firms are tracking a significant evolution in the distribution tactics of the GootLoader malware family. Operators are now using a combination of compromised installers,…
Hackers Sneak Malware Into PCs Using Legitimate Programs
Security researchers have disclosed an active malware campaign that exploits a DLL side-loading vulnerability in a legitimate binary linked to the open-source c-ares library to…
Critical n8n Vulnerability Puts Organizations at Immediate Risk, Warns Pakistan’s National CERT
Pakistan’s National Cyber Emergency Response Team (National CERT) has issued an urgent warning about a critical flaw in n8n, a popular open-source workflow automation platform.…
AI, Geopolitics Driving New Global Cyber Threats: WEF Report
Artificial intelligence, geopolitical tensions, and the rapid rise of online fraud are reshaping the global cybersecurity landscape at an unprecedented pace, according to a new…





























