TeamPCP threat group launched a coordinated supply chain attack compromising 169 npm packages on May 11, 2026. The Mini Shai-Hulud worm targeted TanStack, UiPath, Mistral AI, OpenSearch, and Guardrails AI through self-propagating malware. However, the attack hijacked GitHub Actions workflows using stolen OIDC tokens to publish malicious versions with valid provenance.
The malware includes an obfuscated JavaScript file called router_init.js that profiles execution environments and launches credential stealers. Consequently, the worm targets cloud providers, cryptocurrency wallets, AI tools, messaging apps, and CI systems. Furthermore, stolen data is exfiltrated to filev2.getsession.org domain through the decentralized Session Protocol network.
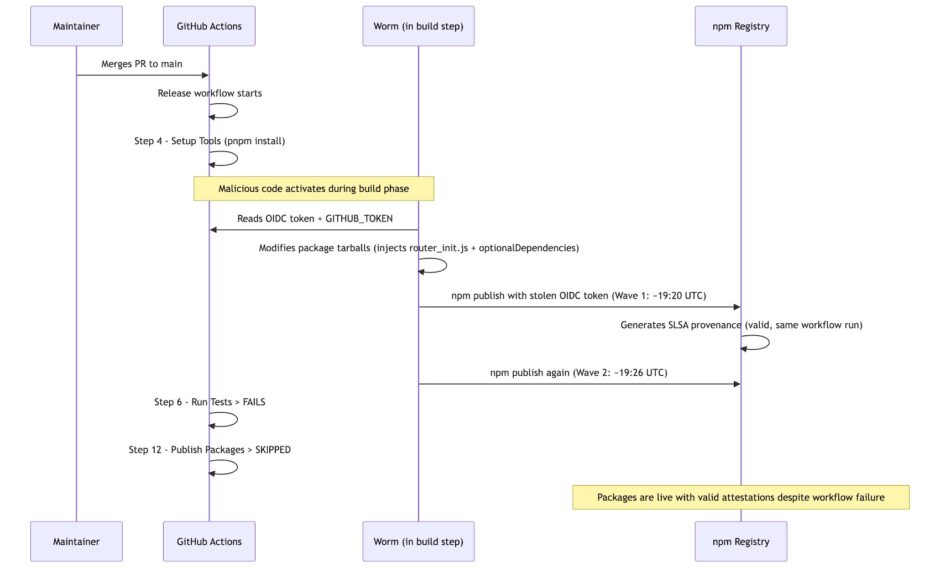
TanStack packages received 12 million weekly downloads making the compromise especially significant for software supply chains. Socket AI Scanner flagged all affected packages within six minutes of publication. Meanwhile, the attack represents the first documented npm worm producing validly-attested malicious packages with SLSA Build Level 3 provenance.
Besides TanStack, the Mini Shai-Hulud campaign has also spread to several other packages, including some in PyPI –
- guardrails-ai@0.10.1 (PyPI)
- mistralai@2.4.6 (PyPI)
- @opensearch-project/opensearch@3.5.3, 3.6.2, 3.7.0, and 3.8.0
- @squawk/mcp@0.9.5
- @squawk/weather@0.5.10
- @squawk/flightplan@0.5.6
- @tallyui/connector-medusa@1.0.1, 1.0.2, and 1.0.3
- @tallyui/connector-vendure@1.0.1, 1.0.2, and 1.0.3
The worm spreads by stealing CI/CD secrets and automatically publishing infected versions of packages maintainers control. TeamPCP is also tracked under aliases DeadCatx3, PCPcat, ShellForce, and CipherForce according to security researchers. Unit 42 documented the group’s partnership with Vect ransomware group based on BreachForums announcements.
Microsoft recently examined the malicious mistralai PyPI package and found that attackers crafted it to download a credential stealer from a remote server, specifically “83.142.209[.]194.” This package has some sneaky features, like country-aware logic that helps it steer clear of Russian-language environments. Plus, it includes a “geofenced destructive branch” that has a 1-in-6 chance of executing rm -rf / if it detects the system is in Israel or Iran.
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux.… pic.twitter.com/9Xfb07Hcia
— Microsoft Threat Intelligence (@MsftSecIntel) May 12, 2026
Developers who installed compromised versions should treat all environment secrets as compromised and rotate credentials immediately. The malware installs persistent monitoring daemons that attempt home directory deletion if tokens are revoked prematurely.




















