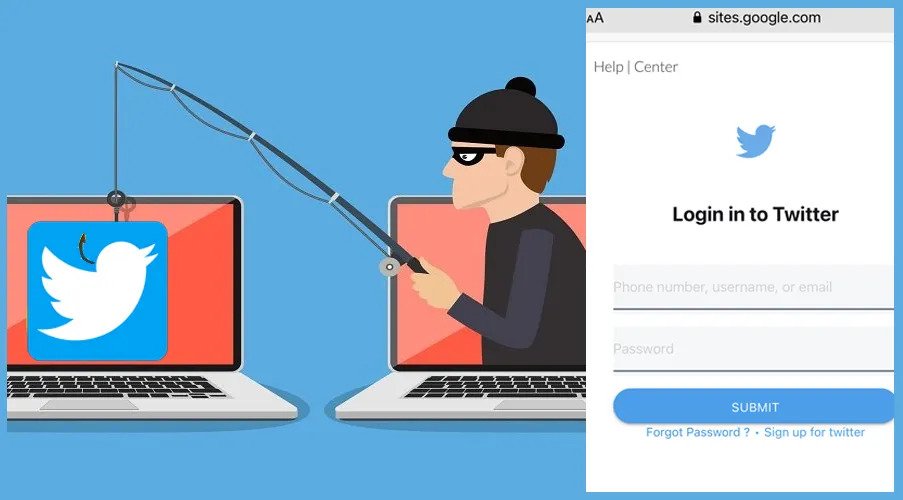
Researchers discovered 3,207 apps on Monday that were leaking Twitter API keys, which hackers can easily exploit to access and hijack Twitter accounts.
According to a report from CloudSEK, 230 mobile apps were found to be leaking all four Auth Creds, which attackers can use to completely take over Twitter accounts and carry out actions such as reading DMs, retweeting, liking, removing or following accounts, acquiring account settings and changing display picture.
Because Twitter has grown to be such a significant social media platform, CloudSEK researchers said that attackers may use Twitter accounts to spread false information in a way that’s not achievable on most other websites. The researchers were especially worried about how dangers and frauds may be incorporated into these activities by hackers, making them seem legitimate to unwary people.
Mobile apps, online platforms and cloud interfaces are generally at risk from poorly secured APIs. More than 30 third-party APIs are often included in modern mobile apps, which hackers may use to steal data, follow users, transmit malware, and execute specialized attacks.
The majority of cloud security mishaps, however, are caused by cloud users misconfiguring APIs or relying too much on unreliable third-party suppliers, not by security flaws on the CSP’s end. The digital safety and trust of today’s users must be protected with greater vigilance, and companies must demand greater transparency from app developers on the program components that put their employees in danger of cyberattack.
The leaked Twitter API keys are one of the many similar cases that have been reported in the past, in which private API keys were unintentionally disclosed, either in an open source version of the program, in a resource that is accessible to the public, or in mobile apps like in this case.
The main difference between this situation and the majority of the prior ones is that, in the majority of cases, when developers release an API key, the application or vendor faces the most risk; an excellent illustration of this is the exposure of AWS S3 API keys on GitHub. Users are actually at the same risk level as the mobile application in this situation since they allowed it to access their personal Twitter accounts. This results in a lengthy list of potential abuses and attack scenarios that are made public as a result of the API and SaaS domains’ rapid expansion.
Although the end users of Twitter may be greatly impacted by this event, this kind of vulnerability is one of the simplest to guard against. It’s crucial to evaluate the device itself, the network layer, and the back-end server when evaluating a mobile app for security flaws.
If API secrets are not encrypted on the device, it would be like wrapping your ATM card in a Post-It note that has your PIN printed on it. In this case, the consequences are far more serious and may prompt attackers to launch defamation or impersonation operations that they may direct at certain Twitter users.