A security firm, CheckPoint, have revealed a vulnerability in the security of Android devices that are powered by Qualcomm Snapdragon chipsets. The security flaw has been named QuadRooter and more than 900 million Android smartphone and tablets are vulnerable to it. Even Samsung’s latest flagship, the Galaxy S7, and the BlackBerry Neon (self-proclaimed “world’s most secure smartphone”) are vulnerable to QuadRooter.
How will it affect you?
If hackers are able to exploit this vulnerability, it will give them complete access to the affected smartphone. This means that all your data, including sensitive images and messages, will be available to the hacker. This is harmful for both individuals and enterprises as well. All the attacker needs to do is to trick you into installing an app on your phone. The worst part is that this app will not even need special permissions for accessing your data!
What measures have been taken to prevent it?
Earlier this year, Qualcomm was notified about these vulnerabilities. The company was able to fix three of the four vulnerabilities through a patch that was publicly made available through Android’s monthly security updates by Google. However, there is one vulnerability that is still resolved and it is expected to be patched up in the next update that comes in September.
How to check if you are affected?
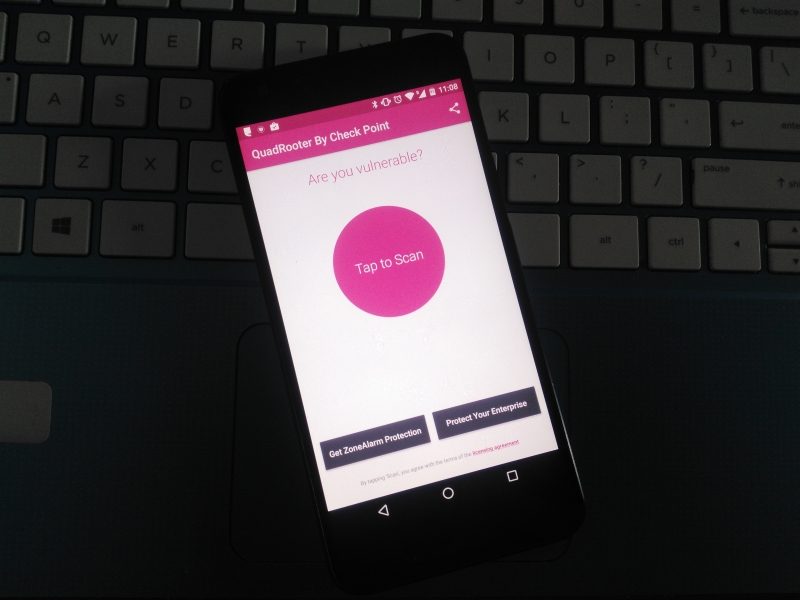
For facilitating the users, Check Point has also launched a free QuadRooter Scanner on the Google Play Store. You can download this app to check if the vulnerability is present in your phone.
What can I do?
For now, all users are requested to avoid installing any malicious apps on their smartphone. Also, keep checking regularly for the monthly security updates on your smartphone to ensure that the issue is fixed with the next update.
Image source – techpp