The general perception is that Apple’s Macs are more secure compared to PCs, especially at the low level of firmware (BIOS). But this perception might be due to the lack of well known attacks rather than better safeguards.
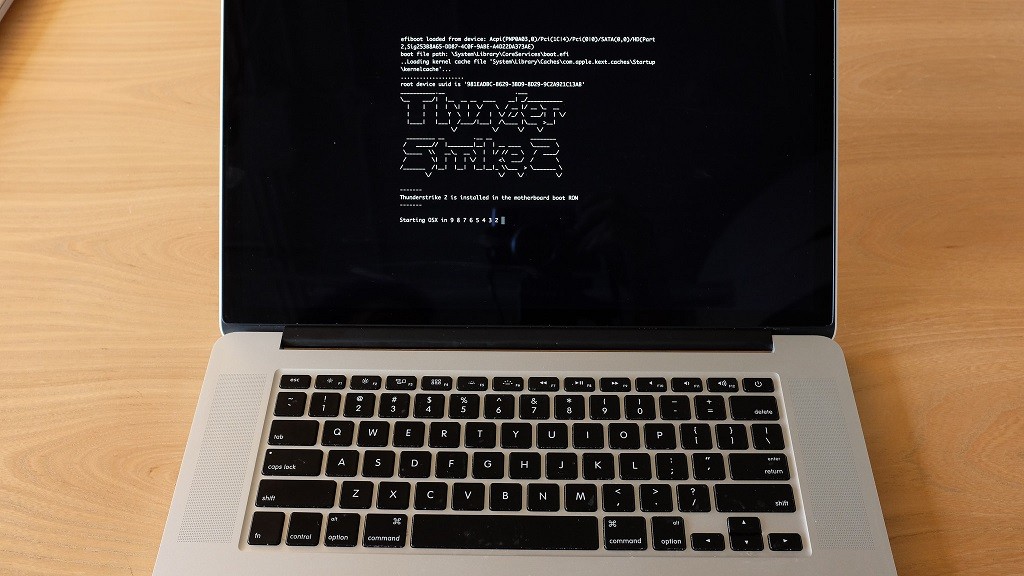
Two computer security researchers, Xeno Kovah and Trammell Hudson have discovered that a number of well known security issues with the firmware of top PC manufacturers can also affect the firmware in Macs. With that, the researchers were able to develop a worm, “Thunderstrike 2” (as a proof of concept) that can spread from one Mac to another even if they weren’t networked. This would be possible because the infected firmware can spread by piggybacking peripherals attached to one Macintosh computer and then another.
A big problem with firmware issues is that they work at a very low level that is hard to detect and work on for regular users. Since the computer’s firmware (or BIOS, the very fundamental software that boots the computer and starts the operating system) is usually on a chip embedded in the motherboard, replacing or formatting your hard drive and re-installing the operating system won’t help. Anti-virus software usually operates at a much higher level and doesn’t have access to the memory that hosts the firmware. Updating firmware requires the older one, so the malicious code can block updates or re-write itself as a part of it.
The only way to get rid of malicious content in a computer’s BIOS would be to flash the chip that holds it. But not might not be possible in many cases.
Thunderstrike 2 only exists in the firmware and can be spread via regular connections or option ROM for computers that are not connected to each other. Option ROM is the peripheral device’s firmware that can be called by the firmware of the computer to which it is connected. An example of such a peripheral on Macs would be Thunderbolt Ethernet adapter, or external SSDs.
The researchers suggest that the firmware vendors can make devices more secure against firmware attacks by signing their firmware and updates cryptographically and modifying the hardware to identify these signatures. Another counter-measure they suggest is that vendors let users access the firmware code and use “checksums” to ensure that the firmware installed is the same as the one vendors supplied and not with malicious modifications. Checksums are already used for checking the integrity of different software and data after download. It involves running the data through an algorithm that creates a small, unique cryptographic code for that specific combination.
Image: popmech.ru




 Warid most likely to be acquired by Mobilink after a long quest
Warid most likely to be acquired by Mobilink after a long quest