Cybersecurity researchers have flagged a new evolution of the GlassWorm malware campaign, which now uses a Zig-compiled native binary to silently spread across all developer IDEs on an infected machine. The technique represents a meaningful escalation from previous GlassWorm variants, which operated within the extension ecosystem. This version attacks at the operating system level and spreads laterally across every compatible editor it can find.
The attack enters through a malicious extension on Open VSX, a package registry used by IDEs that cannot access the official VS Code marketplace. The extension impersonates WakaTime, a widely used developer time-tracking tool. However, it bundles a Zig-compiled native binary alongside its JavaScript code. Because the binary runs as a Node.js native addon, it loads directly into the runtime and executes outside the JavaScript sandbox with full operating system-level access.
Once active, the binary scans the host filesystem for every VS Code-compatible IDE, including VS Code, Cursor, VSCodium, Windsurf, Positron, and several AI-powered coding tools. It then downloads a second-stage malicious extension from a GitHub repository and silently installs it across all detected IDEs using each editor’s own command-line installer. The downloaded file is deleted afterward to remove traces.
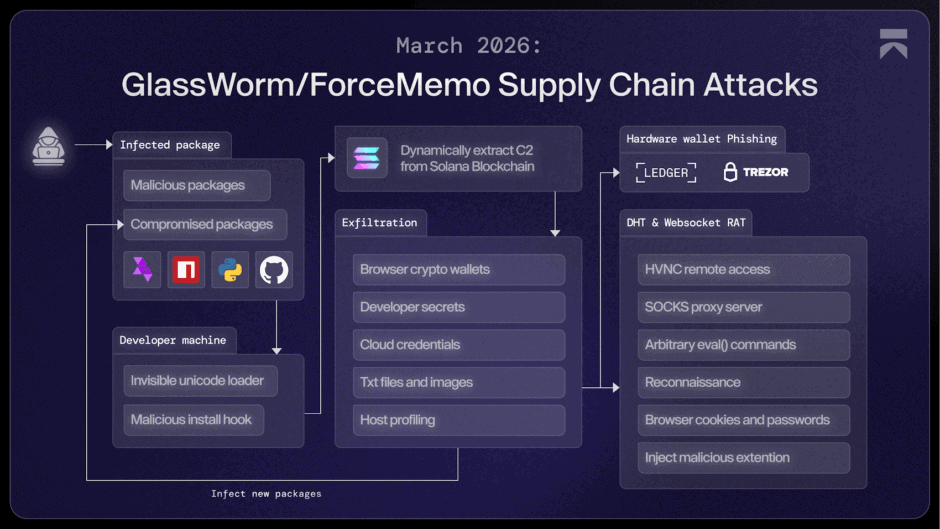
The second-stage extension carries the core GlassWorm payload. It first checks whether the system uses a Russian locale. On non-Russian systems, it contacts a command-and-control server whose address is retrieved from the Solana blockchain, a method designed to make the infrastructure harder to block. It then exfiltrates credentials and sensitive data, installs a persistent remote access trojan, and deploys a malicious Google Chrome extension that logs keystrokes and steals session cookies.
GlassWorm has been active since March 2025, when it first appeared hiding payloads inside invisible Unicode characters in npm packages. Since then, the campaign has compromised hundreds of projects across GitHub, npm, and VS Code. Developers who installed the fake WakaTime extension or see “floktokbok.autoimport” in any IDE extension list should treat the machine as compromised and rotate all credentials immediately.




















