In the past few days, tens of thousands of Facebook accounts have been compromised by a malware that disguises a stress relieving paint program. The malware is being called StressPaint by security researchers. StressPaint was discovered by security researchers of Radware, an American company providing application delivery and cybersecurity solutions.
The domain used for StressPaint shows up as aol.net on search engines and emails by using a Unicode representation. The researchers have indicated that Radware was also available on a domain that was set up to appear as picc.com. It is highly likely that the malware is being promoted in spam emails.
Radware acts as a harmless paint program changing colors and line sizes after it has been installed. However, at its back end, the program starts copying Chrome data of stored cookies and saved passwords for all Facebook accounts accessed on the device. The malware continues to copy the credentials each time a user opens the program and the computer restarts. This data is sent to a command-and-control server.
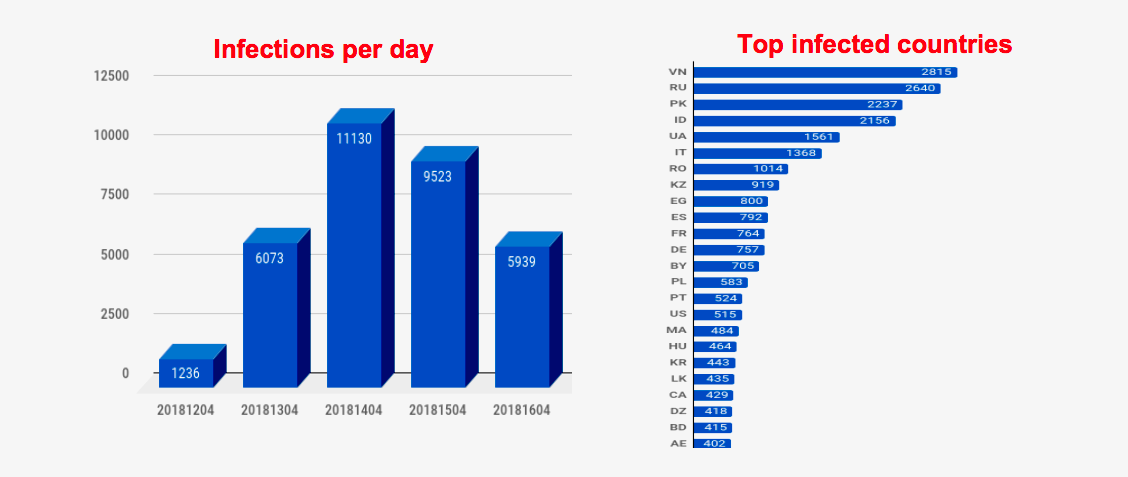
Some researchers gained access to the command server interface discovering that over 40,000 devices were affected, comprising tens of thousands of Facebook accounts. The interface does not only collected login credentials but also kept track of payment details associated with an account, the number of friends and if the account was managing a page. The interface also tried collecting Amazon credentials of victims, however, failed to do so. Another variant of Radware was found in control panels of some devices. The malware is designed to not be detected by antivirus programs. The malware has spread to almost two dozen countries, including Pakistan.
Facebook is investigating this malware attack and taking steps to protect and notify users. Recently, Facebook is one of the 34 companies who has signed an accord to unite against cyber attacks.
Image Source: Ars Technica




 WhatsApp puts a Pakistani drug dealer behind bars
WhatsApp puts a Pakistani drug dealer behind bars